The Electric Power Research Institute (EPRI) conducts research and development relating to the generation, delivery and use of electricity for the benefit of the public. An independent, nonprofit, international organization, EPRI brings together its scientists and engineers as well as experts from academia and industry to help address challenges in electricity, including reliability, efficiency, affordability, health, safety, and the environment. EPRI also provides technology, policy, and economic analyses to drive long-range research and development planning and supports research in emerging technologies. Formed after a historic U.S. blackout in 1965, EPRI was created in response to a growing dependence on electricity and the lack of unified planning and research to support the industry. EPRI meets traditional and emerging challenges with technological innovation, thought leadership, and technical expertise.
With deep research experience and knowledge across the industry, EPRI can contribute to this project through its cyber security and blockchain research programs.
EPRI’s Utility Blockchain Interest Group (UBIG) is a collaborative, utility-focused interest group that leverages EPRI’s subject matter expertise to uncover challenges, benefits, and the potential role of blockchain in the electricity industry. It uses a collaborative approach to accelerate industry learning and applications by sharing use cases, lessons learned, and developing best practices.
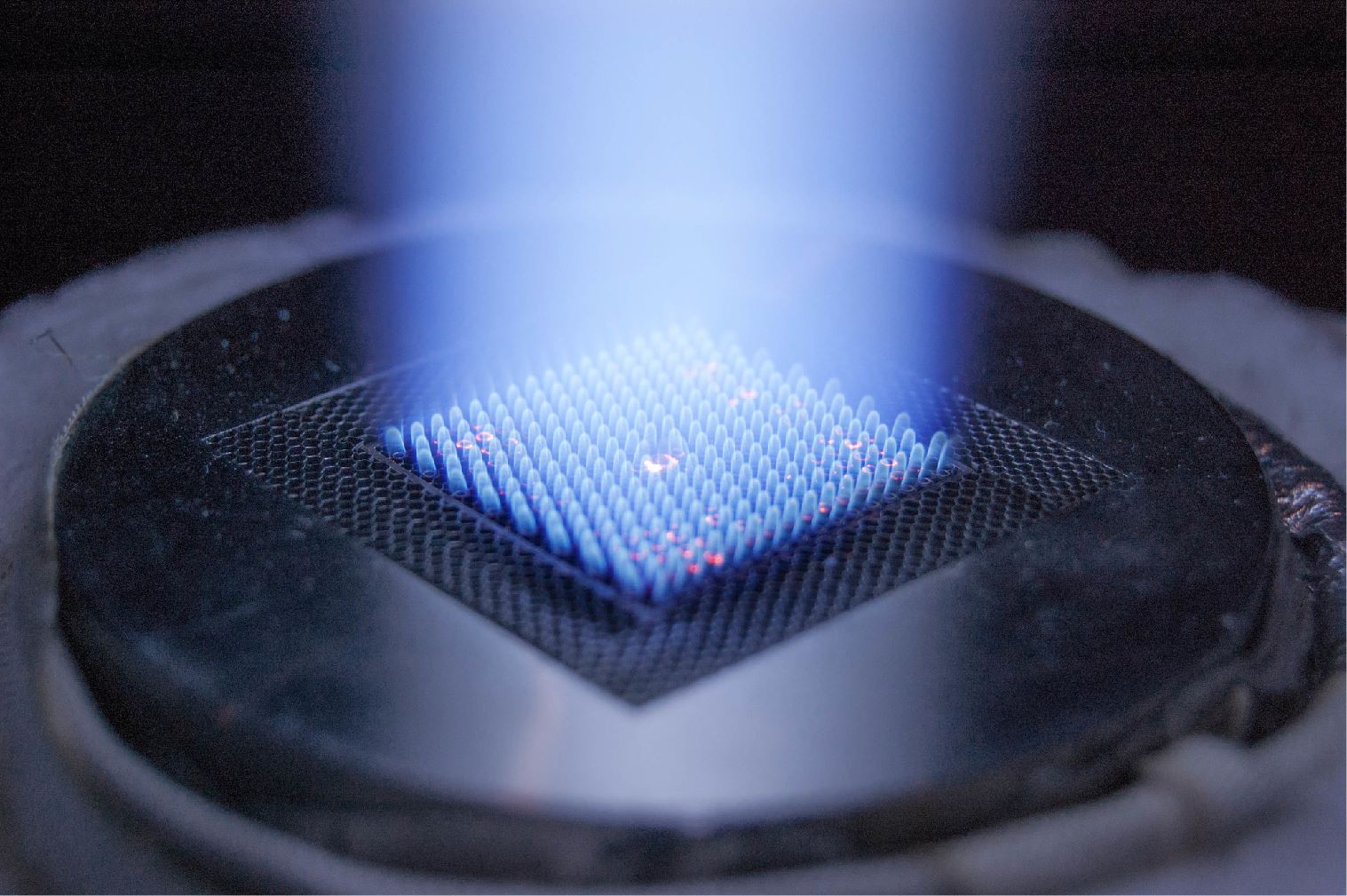
EPRI’s Cyber Security for Generation Assets research includes fossil generation assets, renewable generation assets, and generation interdependencies by ensuring secure generation while maintaining reliability and efficiency. EPRI’s research addresses the specific considerations associated with existing and new generation assets and other critical infrastructure sector’s interfaces with generation.
The program’s research supports protecting assets from a cyber attack, detecting attacks and compromises, and response and recovery efforts.
Research is found at the application level, including implementing field guides and trainings, and at the foundational level which addresses the changing threat landscape, utility processes, and emerging technologies. One example of applied research includes developing a hardware based secure remote access software suite. The integrated solution manages the secure identity provisioning and applies industry cyber security best practices to authenticate and access OT systems.
Current Research
Contact Information: